
People want to extract information, they want to hack people’s accounts, credit cards, and other things. They can do so by becoming Social Engineering experts. It involves various techniques to impact the psychological state of the people’s minds. An attacker can end up convincing a person to give him the information he needs by deceiving them.
ou might have heard the word Social Engineering. But, what exactly is Social Engineering? What are the types of Social Engineering technniques? It can be assumed as a set of techniques primarily intended by the people who want to hack other people or make them do some particular task to benefit the attacker. However, to do this, they don’t want to depend largely on the coding part. Social Engineering scams are the art of deception used by evil minded people to nourish their greed for money or something else.
So, What is Social Engineering?
You might’ve received phone calls or emails from people giving credit card offers. They try to take people into confidence and make them pay a hefty amount to claim the offers. We call such things as a fraud. That’s an example/type of social engineering, where people try confidence tricks on their targets.
It’s not just for financial benefits. Social engineering can be done for other purposes too, for instance, harvesting information from people. It involves playing with people’s mind to get things done.
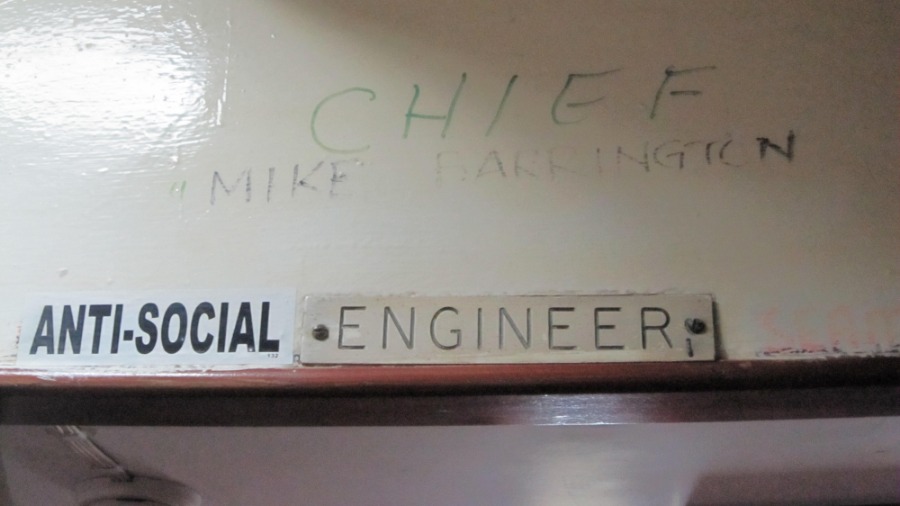
You can find social engineers everywhere. Even your friends sitting next to you concentrating on your keyboard while you type your passwords is a social engineer. It’s just that there is no certification for this thing. So, let’s tell you what are the types of social engineering in detail.
Types of Social Engineering Attacks:
Social engineering can take many forms depending on the medium used to implement it. The medium can be email, web, phone, USB drives, or some other thing. So, let’s tell you about different types of social engineering attacks:

1. Phishing
Phishing is the most common type of social engineering. The attacker recreates the website or support portal of a renowned company and sends the link to targets via emails or social media platforms. The other person, completely unknown of the real attacker, ends up compromising personal information and even credit card details.
2. Spear Phishing
A social engineering technique known as Spear Phishing can be assumed as a subset of Phishing. Although, similar attack, it requires an extra effort from the side of the attackers. They need to pay attention to the degree of uniqueness for the limited number of users they target. And the hard work pays off, the chances of users falling for the false emails are considerably greater in the case of spear phishing.
3. Vishing
Imposters or social engineers can be anywhere on the internet. But many prefer the old fashioned way; they use the phone. This type of social engineering is known as Vishing. They recreate the IVR system of a company. They attach it to a toll-free number and trick people into calling the number and entering their details. Would you agree on this? Most people don’t think twice before entering confidential info on IVR system, do they?
4. Pretexting
Pretexting is another form of social engineering you might’ve come across. It’s based on a scripted scenario presented in front of the targets, used to extract PII or some other information. An attacker might impersonate another person or a known figure. You might’ve seen various TV shows and movies, detectives use this technique to get into places where they’re personally not authorized or extract information by tricking people. Another example of pretexting can be fake emails you receive from your distant friends in need for money. Probably, someone hacked their account or created a fake one.
5. Baiting
If you have seen the movie Troy, you might be able to recall the trojan horse scene. A digital variant of this technique is known as Baiting and it is one of the social engineering techniques used by people. Attackers leave infected USB drives or optical disks at public places with a hope of someone picking it up out of curiosity and using it on their devices. A more modern example of baiting can be found on the web. Various download links, mostly containing malicious software, are thrown in front of random people hoping someone would click on them.
6. Tailgating
Similarly, there are other social engineering techniques, like Tailgating, where a person takes help of an authorized person to get access to restricted areas where RFID authentication or some other electronic barrier is present.
7. Quid pro quo
Another social engineering method Quid pro quo involves people posing as technical support. They make random calls to a company’s employees claiming that they’re contacting them regarding an issue. Sometimes, such people get the chance to make the victim do things they want. It can be used for normal people also.
Quid pro quo involves an exchange of something with the target, for instance, the attacker trying to solve a victim’s genuine problem. The exchange can involve materialistic things such as some gift in return for the information.
How to defend yourself from social engineers?
A few months ago, you might’ve come across the story of Ivan Kwiatkowski. He had sensed a smelly customer support call before it was too late. He managed to fool the so-called executive on the other side and installed ransomware on the attacker’s computer. That could be thought of as a counter attack on such people. You need to be alert when someone asks you to give your information or when some unknown person is giving something to you for free.
Social engineers can also try to hit on the emotional part of people’s brains. They might try to take you on a guilt trip, make you nostalgic, or even try to impact negatively. The situation becomes alarming; people have the tendency to open up in front of the ones trying to give them emotional comfort.
One more thing you must pay attention to save yourself from different types of social engineering scams is what you do on the internet. A person trying to hack into your online account may glance through your Facebook profile and find some clues about the answers to the security questions or even your password.
Mostly, such questions include less important stuff like pet names, school names, birth place, etc. Also, pay attention to what web pages you visit or what files you download. They may contain malicious tools to harvest your information.
However, these are general ways to defend oneself from being exploited by a social engineer. Big organizations have devised more formal methods to deal with such scenarios. This can include things such as conducting regular drills on employees, training them to deal with such situations, and establishing proper methods to identify a legitimate personnel.
So, this was a brief overview of social engineering and their types. If you feel like adding something, drop your thoughts and feedback.
Here’s a bonus video:

Comments
Post a Comment